 An official website of the Pakistan government Here’s how you know
An official website of the Pakistan government Here’s how you know 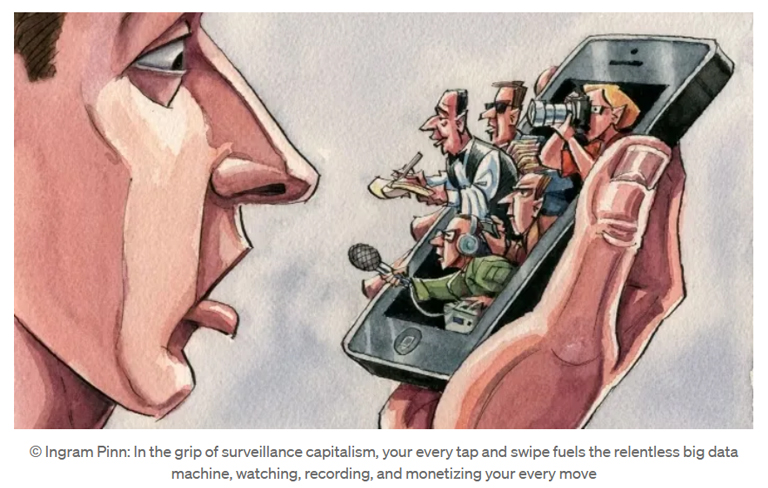
In the winding alleys of economic history, few paradigms have altered the fabric of society as profoundly as capitalism. From the Industrial Revolution’s mechanization to the digital era’s information surge, capitalism has consistently pursued the commodification of every conceivable resource. However, as we navigate the complexities of the 21st century, a more insidious form has emerged — Surveillance Capitalism...
A country's progress mainly depends on the quality of its education system, which determines the direction of growth and prosperity. However, due to a combination of sociocultural factors and individual differences in IQ, students' learning capacities vary widely. The achievement of universal access to high-quality education is seriously hampered by this discrepancy, particularly in developing countries with little funding...

In the digital age, cybercrime isn't just a nuisance anymore; it's a financial time bomb ticking away, threatening to detonate with devastating consequences. The once-distant threat of hackers has become a tangible, immediate danger to financial institutions worldwide. Due to the vast amounts of sensitive data and transactions they handle, financial institutions are particularly vulnerable to these attacks...
In the midst of our glittering technological triumphs, the rise of Artificial Intelligence (AI) stands as a testament to human ingenuity. Yet, as we bask in the glow of our digital creations, a paradoxical shadow looms large: the more we invest in these intelligent systems, the more we risk rendering ourselves hollow. Drawing from John Searle’s philosophical conjectures, T.S. Eliot's haunting verses in "The Hollow Men" and "Choruses from The Rock...

In the ever-evolving landscape of cybersecurity, combating Advanced Persistent Threats (APTs) and safeguarding National Critical Information Infrastructures (NCII) are paramount. Leveraging Artificial Intelligence (AI) has emerged as a strategic necessity, offering advanced analytics, machine learning, and automation techniques across various stages of cybersecurity operations. Here, we delve into the multi-faceted approach of utilizing AI to fortify...
In the annals of philosophical thought, few ideas have been as intriguing and prophetic as Jeremy Bentham's concept of the "Panopticon." Born in the 18th century, Bentham's vision of a panopticon was, at its core, an architectural design for a prison that would facilitate total surveillance of inmates without their awareness. This concept finds new relevance in today's AI-ized and overly digitalized world, as the omnipresence of artificial intell...

In the dynamic realm of digital transformation, one technology stands out for its potential to revolutionize industries: blockchain. With promises of heightened security, transparency, and decentralization, blockchain has captured the imagination of innovators worldwide. However, as with any groundbreaking technology, blockchain presents its own set of cybersecurity challenges. Understanding and addressing these challenges are crucial for ensurin...

As someone who is deeply entrenched in the world of cybersecurity, I have often found myself fascinated by the intricate dance between hackers and their targets. It is like a high-stakes game of cat and mouse, with hackers employing cunning tactics to outsmart even the most fortified defenses. In this blog post, we will delve into the fascinating realm of social engineering, exploring the tactics used by hackers to manipulate individuals and orga...

In today's brave new world, Artificial Intelligence (AI) has seamlessly woven itself into the fabric of our daily lives, transcending traditional boundaries and permeating every facet of human existence. From virtual assistants anticipating our needs to recommendation algorithms shaping our preferences, AI is omnipresent. However, its impact extends beyond the realms of convenience; it has become an indispensable player in the ever-evolving lands...
